SECURITY
Data Erasure: Compliance and Destruction
Every IT asset decommissioning begins with the irreversible destruction of data. Facing GDPR requirements and the criticality of information, WeeeDoIT’s secure data erasure guarantees complete traceability and compliance with the strictest international standards (GDPR, ANSSI, ISO 27001, internal requirements).
SERVICE
Data Erasure by WeeeDoIT
Secure data erasure is an essential step when equipment leaves your IT fleet: resale, recycling, refurbishment, change of use, or simple disposal. At WeeeDoIT, we apply the strictest international standards (NIST 800-88, IEEE 2883-2022, HMG IS5, Secure Erase) to guarantee that your data disappears permanently, while allowing — where possible — equipment to be reused or repurposed.
Our certified software (Common Criteria, ADISA, ISO 27001, ANSSI) guarantees irreversible, verified, and documented erasure.
Our commitment: Secure erasure ensures that no data can ever be restored, neither by specialized tools nor by advanced manipulation. It is a security requirement, but also a pillar of your ITAD, ITAM, compliance, and ESG strategy.
Adapted to All Media Types
HDD, SSD, NVMe, LTO… Each media type requires a specific method: wiping for hard drives, Secure Erase / NVMe Format for SSDs, crypto-shredding for encrypted systems, mechanical destruction for faulty units and LTO tapes. We always apply the right method to the right media — never a generic solution.
Complete Unit-Level Traceability
Each erasure generates a detailed report and a timestamped certificate: serial number, method applied, verification results, final status. This document serves as your proof of compliance during internal audits, GDPR reviews, or regulatory requests.
Zero-Recovery Guarantee
We apply certified erasure methods that make any recovery impossible, even with advanced tools. Each medium is individually verified to validate that 100% of the data has been erased. In the event of failure, the medium is automatically redirected to secure physical destruction.
Device Reuse
Once erasure is validated, the equipment can be reused, refurbished, and repurposed. This reduces your IT costs, extends the lifespan of equipment, and reduces electronic waste. Secure erasure allows you to combine security, performance, and positive environmental impact.
+ 10 000
drives erased and refurbished per year
24h
average time to receive complete certificates
Zéro
data leaks following a WeeeDoIT erasure
100%
of media processed individually
COMPLIANCE
Erasure Methods: Choosing the Right Technique for Each Medium
Secure erasure is not simply formatting. Each medium has its own technical constraints and a unique method to guarantee no data remains. We apply the most appropriate method based on: the condition of the medium (functional, unstable, out of service), its type (HDD, SSD, NVMe, magnetic tape), its previous use (production, finance, HR, sensitive data), and your internal security policy. Here are the methods we use.
Certified Software Erasure
(Wiping) 1 to 3 rewrite cycles of the disk with random patterns or zeros, to make any data unrecoverable, even via specialized tools.
◉ Ideal for: HDDs, traditional servers, workstations..
◉ Benefits: NIST Clear/Purge compliant, allows reuse and refurbishment.
Key point: The standard method for HDD drives in the market.
Manufacturer Erasure
(Secure Erase / NVMe Format) Native manufacturer command that erases an SSD at the hardware level, auaranteeing total erasure.
◉ Ideal for:SATA SSDs, NVMe SSDs, flash arrays.
◉ Benefits: Most reliable method on flash media, required for NIST Purge.
Key point: Essential for functional SSDs before resale or reuse.
Cryptographic Erasure
(Crypto-Shredding) Permanent deletion of the encryption key, instantly rendering all data unreadable, without needing to erase each block.
◉ Ideal for : Virtual machines, encrypted systems, secure appliances.
◉ Benefits: Fast, verifiable, perfect for virtualized environments.
Key point: The most efficient method when data is already encrypted.
Physical Destruction
Irreversible elimination of the medium via shredding, mechanical cutting, or fine destruction when erasure is not possible or not sufficient.
◉ Ideal for: Damaged, non-functional media, or highly sensitive data.
◉ Benefits: NIST Destroy compliant, complete traceability by serial number.
Key point: The only option when software or hardware erasure fails.
STANDARDS
International Standards and Erasure Benchmarks
Erasure standards define recognized methods for permanently deleting data from a storage medium. They serve as a common reference for CIOs, CISOs, and auditors to verify that the operation has been carried out correctly, according to a measurable level of security. By applying them, we guarantee that each erasure respects a clear, traceable, and technically sound framework — and that a compliant erasure certificate can be issued, accepted during internal, ITAD, GDPR, or governance audits.
NIST SP 800-88 Rev.1
nternational reference standard defining Clear, Purge, and Destroy levels for erasure and destruction. Required during audits or ITAD projects. Applicable to HDDs, SSDs, and magnetic tapes. The foundation of all our erasure procedures.
ISO/IEC 27040
Standard dedicated to storage security, covering data management, protection, and destruction. Reinforces DLP and ITAD policies. Used to frame internal governance. Relevant for sensitive organizations.
DoD 5220.22-M
Historical method based on multiple overwrite passes to delete data. Still required in certain contracts. Applicable primarily to HDDs. Alternative when a specific standard is required.
Secure Erase / NVMe Format
Hardware erasure methods directly integrated into SSDs, guaranteeing complete erasure of all cells. Essential for Purge-level erasure. Recommended for all functional SSDs. Indispensable for eliminating inaccessible blocks.
QUALITY
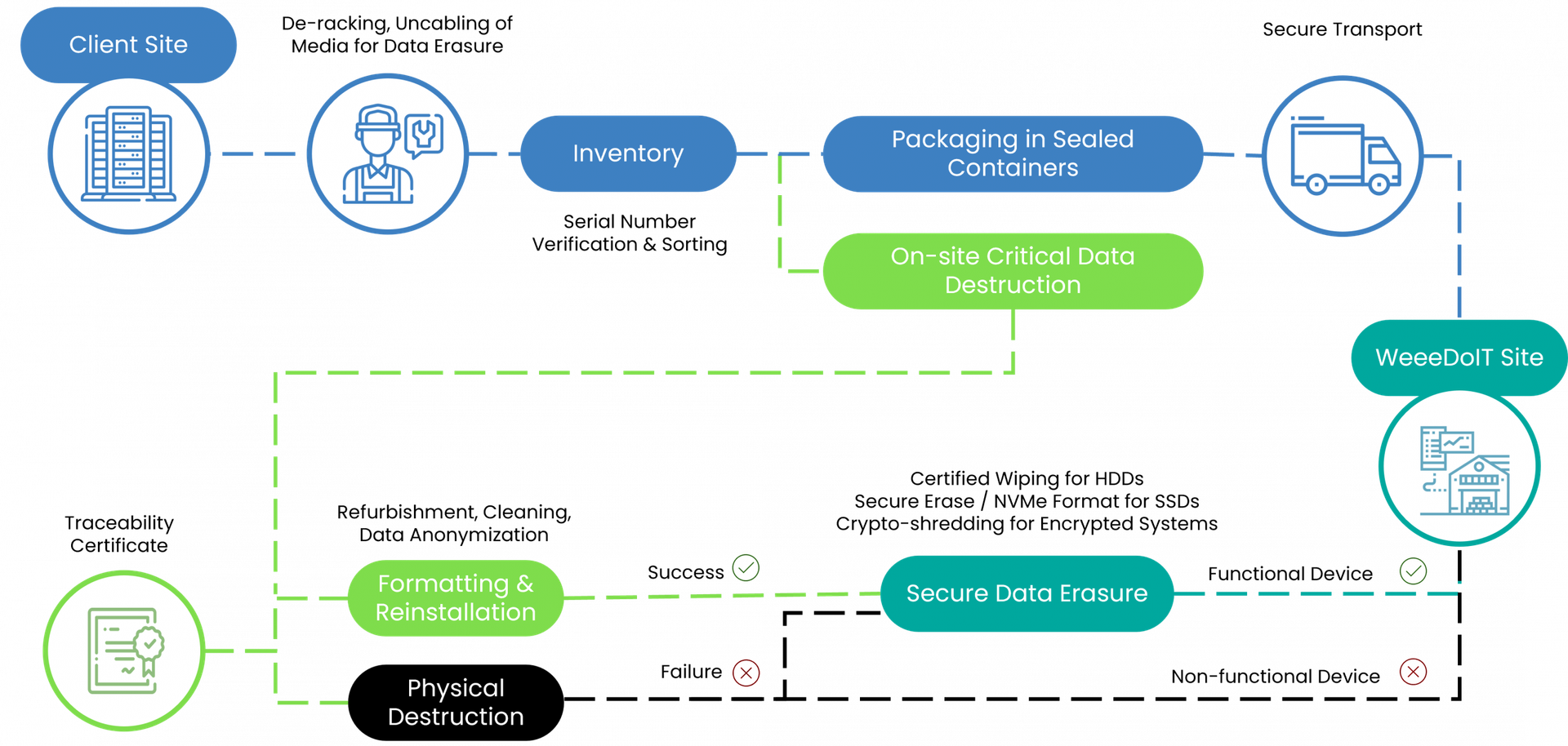
Our Erasure Process, Step by Step
TRACKING
The Erasure Certificate: Your Auditable Proof
Every data erasure intervention concludes with the delivery of an essential document: the Erasure Certificate.
- Company and site name
- Date and time of erasure
- Unique serial number of each processed medium
- Erasure method applied (e.g., NIST Purge)
- Software name and version used
- Success status (Pass/Fail)
This certificate is your proof of due diligence in the event of an audit (GDPR, ISO 27001) and attests to your commitment to data security.
Serveurs
Hard Drives
SSD
NVMe
Bandes magnétiques
What sets WeeeDoIT apart

Multi-standard certified (NIST, DoD, ISO)

GDPR, REEN, and ISO 27001 compliance

Zero-leak → zero-risk commitment

On-site or in-workshop secure erasure
FAQ
Questions on Secure Data Erasure
What is the difference between simple deletion and secure erasure?
Simple deletion removes visible files but leaves residual or “ghost” data still present on the medium. These fragments can be recovered with disk reading tools, exposing your sensitive information. Secure erasure applies certified protocols (multiple overwrites, binary verification, complete reformatting) to guarantee permanent deletion, making any recovery impossible.
Which types of media need to be erased?
All equipment likely to contain data, including: HDDs and SSDs, USB drives; complete servers (including NAS, SAN, DAS arrays); PCs, laptops, and workstations; switches, routers, firewalls (internal memory); copiers, multifunction printers, network scanners; embedded systems, network appliances, or IoT; professional smartphones and tablets. In short: any equipment containing a storage medium, even temporary, must be erased before transfer, resale, or recycling.
What standards and certifications guarantee your service's compliance?
NIST 800-88 Rev.1, DoD 5220.22-M, ISO 27001, GDPR, RGS and REEN. We work with certified publishers, all compliant with European ITAD requirements.
Do you operate on-site or must equipment be sent to your workshop?
All options are available: on-site intervention, secure transport to our workshops, or client shipment. Each option includes the same level of traceability, control, and certification.
What erasure software do you use?
Exclusively internationally accredited solutions: Blancco, BitRaser, KillDisk, and other tools compliant with DoD and NIST standards.
How long does a complete erasure take?
15–30 min for an SSD under 256 GB; 1–3 hours for a standard 1–4 TB HDD; up to 24 hours for large storage arrays or RAID clusters.
Do you provide an erasure certificate for each medium?
Yes. Each erasure is individually recorded with: medium ID (serial number, model, type), date/time/technician, software and protocol used, and final status. This certificate constitutes legal, auditable proof.
Can the operation be supervised?
Yes. Interventions can be carried out in the presence of your teams (CIO, CISO, internal auditors). The process is transparent, documented in real time, and can be filmed upon request.
What happens if the medium is defective and cannot be erased?
We proceed with controlled physical destruction: degaussing, mechanical drilling, shredding, or complete fragmentation. A destruction certificate is then issued in place of an erasure certificate.
